HIPAA Assessment Criteria
Risk Assessments and OCR Audits
There are two possible interpretations of the term “HIPAA assessment criteria” – the criteria that should be considered when conducting risk assessments, and the HIPAA Audit Protocol. It is necessary to understand both interpretations in order to be HIPAA compliant, and to pass inspections conducted by the U.S. Department of Health & Human Services´ Office for Civil Rights (OCR).
HIPAA Risk Assessments
HIPAA risk assessments are a necessary and ongoing process to identify security vulnerabilities and risks to the integrity of Protected Health Information (PHI). They should be conducted on a regular basis by a “Privacy Official” – an employee or outside specialist assigned to the task by a healthcare organization of HIPAA-covered entity.
Using the HIPAA assessment criteria contained within the HIPAA Privacy Rule, the Privacy Official should investigate how PHI is managed in relation to:
- Access to PHI
- Privacy and confidentiality
- Marketing, fundraising and research
- The minimum necessary rule
- Disclosures of PHI and breach notification
- Employee training for HIPAA compliance
- Business Associate agreements
The HIPAA risk assessments required under the HIPAA Security Rule are far more extensive. Privacy Officials need to consider the administrative, physical and technical requirements of the HIPAA Security Rule, such as audit and authentication controls, the security of the facility in which PHI is stored, and how PHI is communicated electronically between medical professionals.
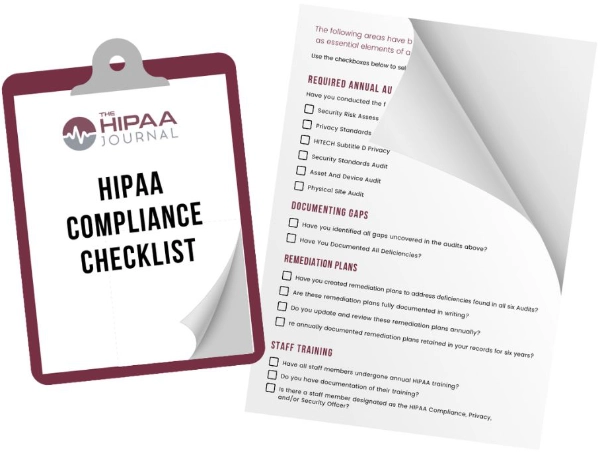
Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
HIPAA Journal Privacy Policy
Many of these requirements revolve around preventing unauthorized access to PHI while it is at rest or in transit. Consequently access to workstations, the use of personal mobile devices and message accountability come high on the HIPAA assessment criteria. Monitoring when PHI is accessed and how it is used is also important to identify security vulnerabilities and risks to the integrity of PHI.
HIPAA Audit Protocol
The current HIPAA Audit Protocol was developed by OCR following a 2012 round of audits that identified an alarming lack of compliance. Audited healthcare organizations registered numerous violations of the HIPAA Breach Notification Rule, Privacy Rule and Security Rule – with the latter resulting in the highest number of violations. Consequently, the current HIPAA assessment criteria for OCR audits focuses on seven specific areas:
- Notice of privacy practices for PHI
- Rights to request privacy protection for PHI
- Access of individuals to PHI
- Administrative requirements
- Uses and disclosures of PHI
- How PHI is amended
- Accounting of disclosures
Following the 2012 round of audits, the OCR issued action plans to help those healthcare organizations that had failed the audit achieve compliance. A second round of audits is expected soon and it is not anticipated that the OCR will be so lenient. Any covered entity that does not fulfill the HIPAA compliance criteria faces financial penalties, sanctions, potential loss of license and even criminal proceedings for failing to secure PHI.
How Secure Messaging Meets the HIPAA Assessment Criteria
Secure messaging meets the HIPAA assessment criteria by operating via a secure cloud-based environment. The solution works by creating a secure and encrypted communications network for healthcare organizations that can only be accessed by personnel fulfilling the ID authentication procedure.
Safeguards exist to prevent PHI being deliberately or accidently sent outside of the network or saved to an external hard drive. Each message sent via the secure messaging platform is acknowledged with a delivery notification and by a read receipt once opened and read. This ensures that each message is received by the correct recipient(s) and ensures 100% message accountability.
To comply with the HIPAA assessment criteria, further security measures automatically log personnel out of the network after a period of inactivity, messages have “lifespans” attached to them so that they auto-delete, and administrators can remotely PIN-lock secure messaging apps if a user´s mobile device is lost or stolen.